Forrester’s CISO budget priorities include API, supply chain security
Join our daily and weekly newsletters for the latest updates and exclusive content on industry-leading AI coverage. Learn More
Going into 2025, safeguarding revenue and minimizing business risks must dominate CISOs’ budgets, with investments aligned with business operations driving priorities.
Forrester’s latest budget planning guide for security and risk clarifies that securing business-critical IT assets needs to be a high priority going into next year. “The budget increases that CISOs will receive in 2025 should prioritize addressing threats and controls in application security, people and business-critical infrastructure,” writes Forrester in the report.
CISOs must double down on threats and controls to get application security rights, secure business-critical infrastructure and improve human risk management. Forrester sees software supply chain security, API security and IoT/OT threat detection as core to business operations and advises CISOs to invest in these areas.
Delivering revenue gains by protecting new digital businesses while keeping IT infrastructure safe on a tight budget is a proven way for CISOs to advance their careers.
Treat cybersecurity as a business decision first
The most valuable takeaway from Forrester’s planning guide is that cybersecurity investments must be considered a business decision first. The report’s key findings and guidelines underscore how and why CISOs need to make trade-offs on tools and spending to maximize revenue growth while driving solid returns on their investments.
Forrester calls for CISOs to take a hard look at any app, tool, or suite contributing to tech sprawl and drop it from their tech stacks when adding new technologies.
Critical insights from Forrester’s budget planning guide for security and risk include the following:
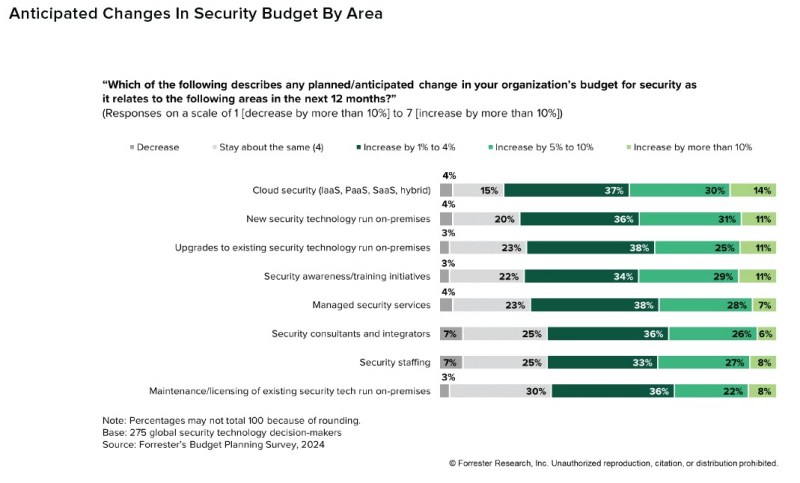
- 90% of CISOs will see a budget increase next year. Cybersecurity budgets are, on average, just 5.7% of IT annual spending. That’s thin, given how broad a CISO’s role is to protect new revenue streams and fortify infrastructure. Forrester cites their 2024 Budget Planning Survey 2024 in the guide, predicting that budgets will continue increasing for the next 12 months. Ten percent anticipate an increase of more than 10% in the next 12 months. One-third expect an increase between 5% and 10%, and almost half expect a modest increase between 1% and 4%. Only seven percent of the budgets will stay the same, and just three percent anticipate reduced budgets in 2025.

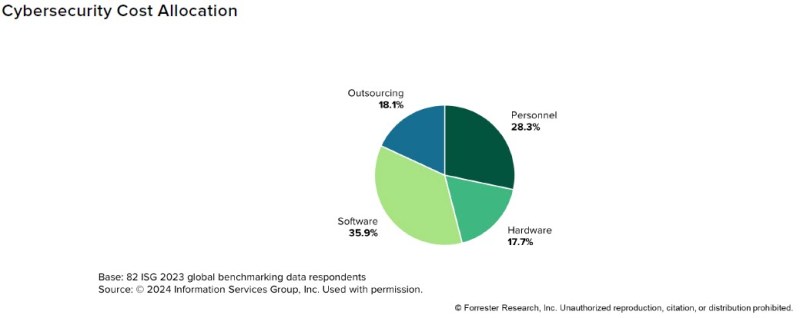
- Get in control of tech sprawl now. Tech sprawl is the silent killer of budget gains, Forrester warns. CISOs, on average, are seeing just over a third of their budgets come from software, doubling what they spend on hardware and also outpacing their personnel costs, according to a recent ISG study. “To combat the genuine issue that already plagues security leaders — tech sprawl — we recommend taking a conservative approach to introducing new tools and vendors with this pragmatic principle: Don’t add something new without getting rid of something else first,” writes Forrester in the report.
Source: Forrester 2025 Budget Planning Guide For Security And Risk Leaders
- Cloud security, upgraded new security technology run on-premises, and security awareness/training initiatives are predicted to increase security budgets by 10% or more in 2025. Notably, 81% of security technology decision-makers predict their spending on cloud security will increase in 2025, with 37% expecting a 5-10% increase and 30% expecting a more than 10% increase. Cloud security’s high priority reflects the essential role that cloud environments, platforms, and integrations play in the overall security posture of enterprises. As more enterprises adopt and build internal platforms and apps across IaaS, PaaS, and SaaS, cloud security spending will continue to grow.
Defending revenue starts with APIs and software supply chains
A core part of every CISO’s job is finding new ways to protect revenue, especially digital-first initiatives enterprise devops teams are working overtime to get out this year.
Here are their suggested priories from the report:
Hardening software supply chain and API security is a must-have. Making the argument that the complexity, variety and volume of attack surfaces are proliferating across software supply chains and API repositories, Forrester emphasizes that security is urgently needed in these two areas. A staggering 91% of enterprises have fallen victim to software supply chain incidents in just a year, underscoring the need for better safeguards for continuous integration/deployment (CI/CD) pipelines. Open-source libraries, third-party development tools, and legacy APIs created years ago are just a few threat vectors that make software supply chains and APIs more vulnerable.
Malicious attackers often look to compromise open-source components with wide distribution, as the Log4j vulnerability illustrates. Defining an API security strategy that integrates directly into DevOps workflows and treats the continuous integration and continuous delivery (CI/CD) process as a unique threat surface is table stakes for any enterprise doing DevOps today. API detection and response, remediation policies, risk assessment, and API usage monitoring are also urgent for enterprises to better secure this potential attack vector.
IoT sensors continue to be an attack magnet
Internet of Things (IoT) is the most popular attack vector attackers use to attack industrial control systems (ICS) and the many processing plants, distribution centers and manufacturing centers that rely on them daily. CISA continues to warn that nation-state actors are targeting vulnerable industrial control assets and today three new industrial control systems advisories were published by the agency.
Forrester’s Top Trends In IoT Security In 2024, published earlier this year and covered by VentureBeat, found that 34% of enterprises that experienced a breach targeting IoT devices were more likely to report cumulative breach costs between $5 million and $10 million compared to organizations that experienced cyberattacks on non-IoT devices.
“In 2024, the potential of IoT innovation is nothing short of transformative. But along with opportunity comes risk. Each connected device presents a potential access point for a malicious actor,” writes Ellen Boehm, senior vice president of IoT Strategy & Operations for Keyfactor. In their recent IoT security report, Digital Trust in a Connected World: Navigating the State of IoT Security, Keyfactor found that 93% of organizations face challenges securing their IoT and connected products.
“We’re connecting all these IoT devices, and all those connections create vulnerabilities and risks. I think with OT cybersecurity, I’d argue the value at stake and the stakes overall could be even higher than they are when it comes to IT cybersecurity. When you think about what infrastructure and types of assets we’re protecting, the stakes are pretty high,” Kevin Dehoff, president and CEO of Honeywell Connected Enterprise, told VentureBeat during an interview last year.
“Most customers are still learning about the state of affairs in their OT networks and infrastructure. And I think there’s some awakening that will be done. We’re providing a real-time view of OT cyber risk” Dehoff said.
Ensuring IoT device access is protected using zero trust is a table stake for reducing the threat of breaches. The National Institute of Standards and Technology (NIST) provides NIST Special Publication 800-207, which is well-suited for securing IoT devices, given its focus on securing networks where traditional perimeter-based security isn’t scaling up to the challenge of protecting every endpoint.
Pragmatism needs to dominate CISOs’ budgets in 2025
“Too many tools, too many technologies and not nearly enough people continue to be the theme in a fragmented and technology-heavy cybersecurity vendor ecosystem,” Forrester cautions.
Treating cybersecurity spending as a business investment first is a priority Forrester sees its clients needing to embrace more, given how that message is emphasized throughout the guide. The message is to trim back on tech sprawl, which they have delivered before regarding the need to consolidate cybersecurity apps, tools and suites.
It’s time for cybersecurity to be funded as a growth engine, not just one used for deterrence alone.
CISOs can balance the scales by looking for an opportunity to elevate their role to a CEO direct report and, ideally, be on the board to help guide their companies through an increasingly complex threat landscape.
Source link